How to Hack iPhone Passcode: Useful Tips to Make It Easy
Forgot your iPhone passcode without ever writing it down?? Does a broken screen prevent you from entering it? Or maybe you need access to hack someone’s phone? We will show you what you can try out to hack iPhone passcode without anyone knowing and how to do it correctly:
- Activate the recovery mode
- Use Find My iPhone
- Access iCloud backup
- Trick Siri
- Utilize forensics software
- Make use of keyloggers & apps
We will cover different methods, from Apple’s built-in features to installing spy software. Whether these methods will do the trick for you mostly depends on your iOS version. Read on to learn more.
How to Hack iPhone Passcode with Built-In Apple Features
How to hack someone’s phone efficiently? In some scenarios, you don’t need to look far to hack iPhone passcode. Even Apple firmware leaves loopholes in security features in case the owner forgets the combination. And we’re about to explore these passcode hack options.
How to Unlock iPhone Without Knowing the Password Using Recovery Mode
If you forgot your iPhone/iPad password, your device is reduced to an expensive doorstop.
However, you can unlock the iPhone lock screen and perform a passcode hack to restore access using the recovery mode (aka DFU mode or device firmware update) method and hack the iPhone passcode without worry. It will erase iPhone user data, but that shouldn’t be a problem if you back up regularly. Here’s how to hack iPhone passcode with iTunes:
- Open Finder on your Mac or iTunes on your PC. If you don’t have iTunes, download and install it first.
- Ensure that your iOS device isn’t connected to the computer.
- Find your iOS device model below and proceed as follows.
How to Bypass iPhone Lock Screen on iPhone 8 and 8 Plus, iPhone SE 2, iPhone X, iPhone 11 or later
- Press and hold the Side button and either Volume button until the power off slider appears;
- Drag the slider to turn off your locked iPhone and connect it to the PC while holding the Side button;
- Hold the button until you see the recovery mode icon.
How to Bypass iPhone Lockscreen for iPhone 7 and 7 Plus
- Press and hold the Side button until the power off slider appears;
- Drag the slider to turn off your phone and connect it to the computer while holding the Volume down button;
- Hold the button until you see the recovery mode screen.
- Press and hold the Side or Top (power) button until the power off slider appears.
- Drag the slider to turn off your device and connect it to the computer while holding the Home button;
- Hold the button until you see the recovery mode activated.
How to Bypass Passcode on iPad with Face ID
- Press and hold the Top button and either Volume button until the power off slider appears;
- Drag the slider to turn off your locked iPad and connect it to the PC while holding the Top button;
- Hold the button until you see the recovery mode sign.
- An iTunes dialog box will now present you with two options: Restore or Update. Click Restore.
- iTunes will download and install the latest iOS version to your Apple device. It should take not more than 15 minutes.
- If it takes longer than that, the device will exit recovery mode, and you’ll have to repeat the whole process.
- Once installation completes successfully, your device should power on. It is now restored to factory settings and ready for use.
iPhone 7 Passcode Unlock with iTunes
This is another handy way to remove the passcode on the lock screen and access someone’s iPhone device. And, you can easily hack an iPhone passcode with iTunes. Here’s what you should do:
- Connect your iPhone device to your computer and open iTunes.
- Once iTunes detects the target iPhone, click on the device icon.
- Open the Summary tab from the left side of the panel.
- Choose the Restore iPhone option, click on it, and wait for the device to restart.
- Once done, you will remove the passcode, and you will be able to unlock your iPhone 7 even if you have previously forgotten the code.
iPhone Passcode Hack via Find My iPhone
If you don’t have a computer or the hack iPhone passcode with iTunes method seems to be a bit of a hassle, Find My iPhone is a reliable alternative to hacking iPhone passcode. Although the app was designed to track lost iOS devices, users can also remotely erase iPhone data and the screen password in one go.
For you to get rid of the screen lock, this free built-in Apple service should be activated beforehand. The phone must be linked to the iCloud account and connected to the internet. You also need to know the iCloud credentials or at least be able to guess them via social engineering technique (using your knowledge about the account’s owner, like their birthdate, pet’s name, favorite character, etc.).
If those conditions are met, here’s what you should do next:
Step 1: Visit the iCloud.com website on any other device. If you have another iOS device, launch the Find My iPhone app instead.
Step 2: Enter the credentials of the account linked to the iPhone you want to unlock and log in.
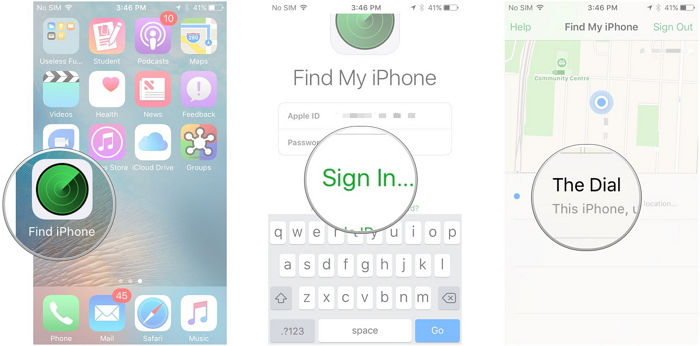
Step 3: Select the target iPhone on the list of connected devices.
Step 4: Now, you should be able to see the device’s real-time location. Tap the Actions button below.
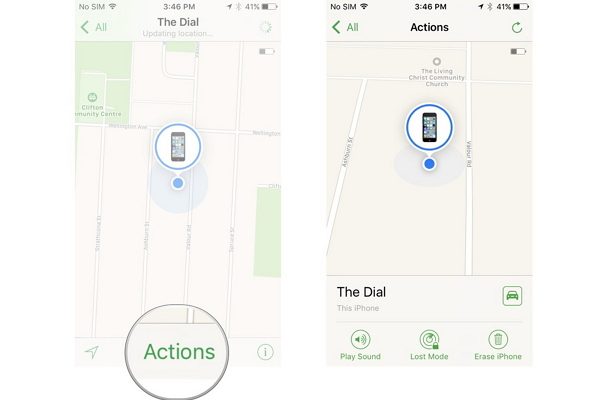
Step 5: Choose Erase iPhone and confirm.
It won’t be long before the device is reset and the screen lock is gone.
Hack iPhone Passcode Using the iCloud Backup
Do you want to access data on the phone rather than use it? You won’t even have to hack the iPhone passcode if you have the target’s Apple ID.
→ Log into the iCloud of your target from any other device and see if they have created the iPhone backup.
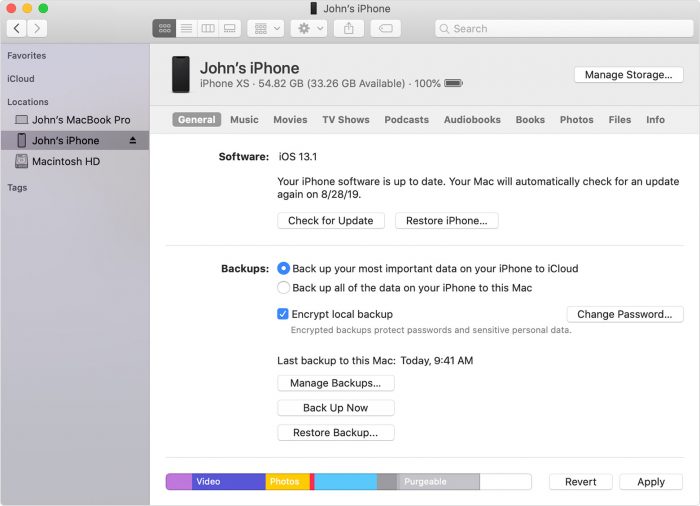
→ Restore it.
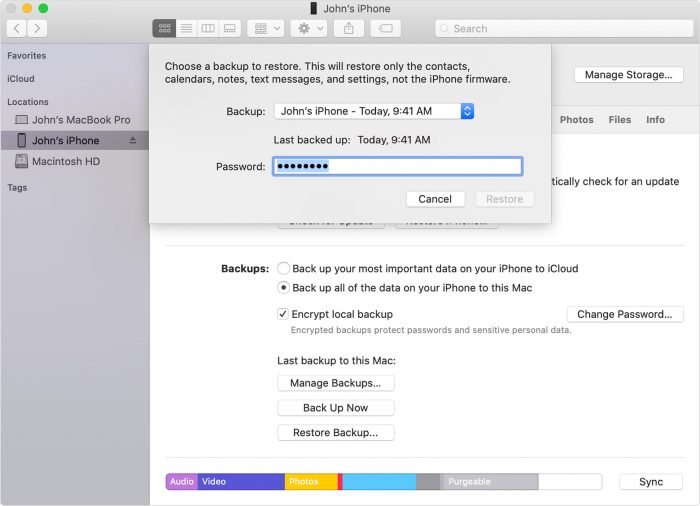
And get the following info:
- History of incoming and outgoing calls
- All contacts
- Photos, videos, documents, and other files from iCloud Drive
- iMessage & email correspondence that person is storing on their iPhone.
- List of installed applications
- Target iPhone’s live location
How to Unlock iPhone Without Passcode Using Ask Siri
If you have a locked iPhone still running on iOS 8-11, it is possible to activate Siri and unlock the iOS device without a factory reset:
- Press & hold the Home button for a few seconds to activate Siri.
- Ask Siri, “What’s the time now?” the local time will be promptly displayed on the screen.

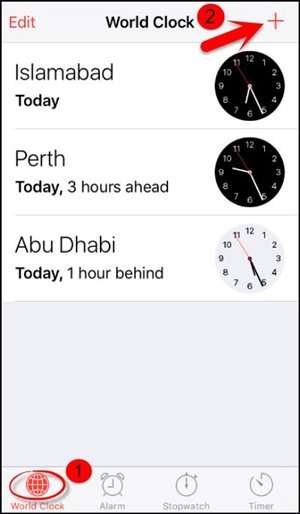
- Enter the World Clock menu by tapping on the clock icon.
- Add another world clock by clicking “+.”
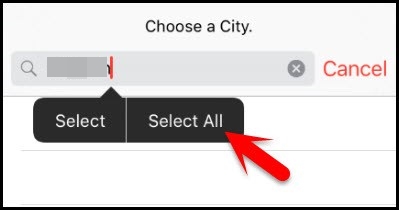
- Tap the search box on your screen and type some random characters.
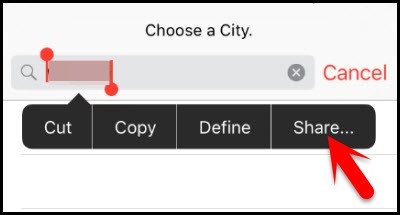
- Select all the characters and then copy them.
- In the listed options, select Share and then select the Message icon from the dropdown.
- Paste the copied characters in the To field in the New Message window.

- Press the Home button after about two seconds.
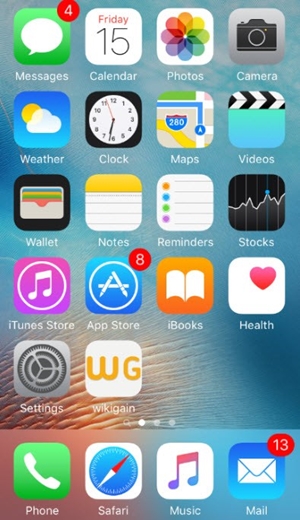
- Your Home screen will then appear. You’ll have successfully bypassed the iPhone passcode without DFU mode or Face/Touch ID.
However, there is a way to hack the iPhone passcode on iOS 12.0 that will allow you to browse the contacts and photos on the locked iPhone of your target. This method is best explained here:
How to Hack iPhone Passcode with Third-Party Software
Although Apple devices are considered extremely safe, there are some security vulnerabilities that professional hackers and ordinary people can use.
Starting with iOS 8.0 and ending with iOS 10.2 beta 3 versions, there are system breaches that allow you to bypass passcode protection or Face/Touch ID.Modern hacking software providers are actively using them to hack the iPhone passcode.
Let us introduce you to the most effective options.
Bypass iPhone Passcode Using Forensics Software
Elcomsoft Phone Passcode Breaker (EPPB) and Elcomsoft iOS Forensic Toolkit (EIFT) are programs that will help you to do the passcode hack within several steps.
Aside from the provider mentioned above, Blacklight is world-class forensics software that is just as effective in bypassing passcodes for iOS devices.
Forensics software allows users to get an image of the communicator system automatically saved on iCloud. When having this file, you can restore any data you require.
The 1st spyware works to decrypt iPhone data; the 2nd one is needed to transfer the entire iPhone system image from the communicator (iCloud) to the computer.
The developer of the EPPB product has created this program for law enforcement professionals. It monitors the distribution of the product and attempts to obtain it.
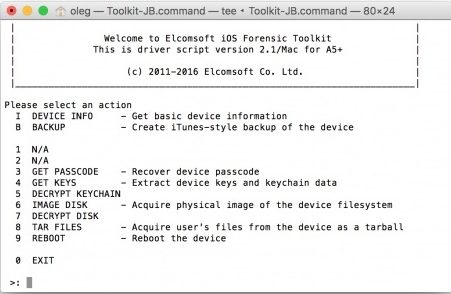
For such programs to work, you need to:
- Get a target’s Apple ID with a password.
- Choose encryption keys to extract all the files from the image.
- Output the discovered code of four characters within the additional window field.
- Receive the code as a text message on iMessage or a pop-up notification.
The programs wiretap the code of a 64-bit ARM processor that you can use for the iPhone hack (the program will save the image to another device in a standard format by iTunes.
The system image downloaded from iCloud is opened using EPPB; you can access all files by selecting suitable keys). As a result, you can hack any data on target iPhones. With these tools, you can export large volumes of data without needing a passcode.
While most forensic software is not available to the public, applying for a license will enable you to get your hands on it and get an inside look at all data on an iPhone.
Hack iPhone Passcodes of All Sorts with iMyfone Lock Wiper & Co
With smart software like iMyfone Lock Wiper, hacking the iPhone passcode is as easy as breathing. The app works with all Apple devices running on iOS 12 and earlier.
It unlocks screen locks: Screen Time, 4-digit and 6-digit passcodes, Face ID, and Touch ID. Boasting efficient tech support, a comprehensive guide, and a risk-free 30-day money-back guarantee, iMyfone Lock Wiper is worthy of your attention.
Step 1: Download iMyFone LockWiper software to your PC
Step 2: Choose “Unlock Screen Passcode,” click “Start.”
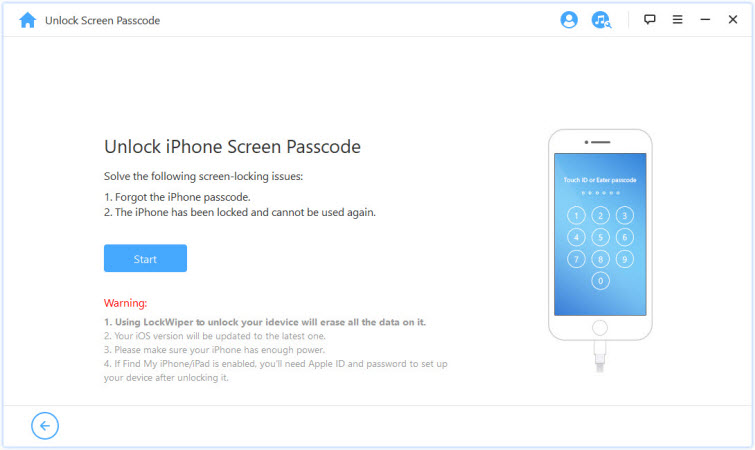
Step 3: Connect your iPhone to the computer.
Step 4: The software detects your iOS device automatically and displays its data. Select the information and files you need and click “Download.”
Step 5: After completing the download process, click “Start to Extract.”
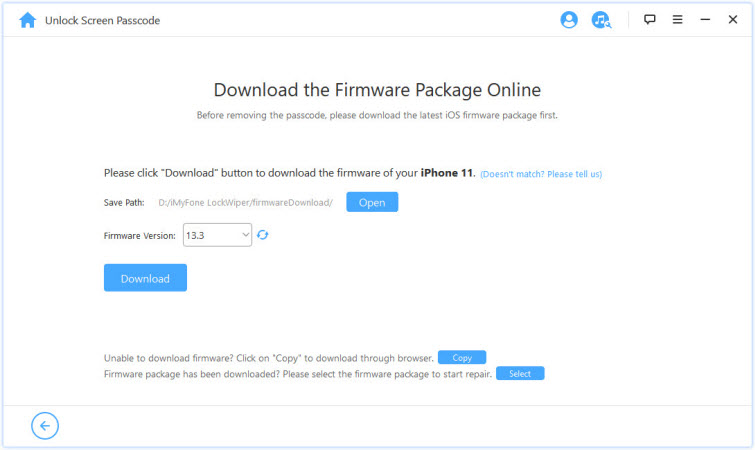
Step 6: Once extraction is finished, click “Start Unlock” and confirm.
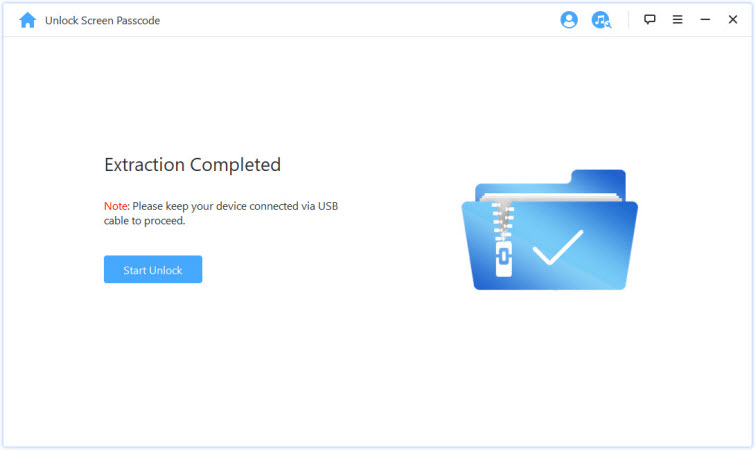
The whole process takes just a few minutes, depending on the volume of data you’re extracting. As a result, you can now use the iPhone as if it were a new one.
The decent alternatives for this program are Tenorshare 4uKey (up to iOS 11) and Dr. Fone (up to the latest iOS 13!), which work in basically the same way but may be a better option for you in terms of pricing.
Keylogger Spyware – This Is How You Hack iPhone Passcode Remotely
Keylogger is short for keystroke loggers. It’s a special invisible spying software that captures everything the target device’s owner types, including the iPhone passcode.
One of the market leaders is mSpy hacking software which also got onto our list of top-notch keyloggers. It’s easy to install and works in stealth mode and remotely. Every single click and tap is now plainly visible.
It will send you records of text messages (even already deleted ones), IM chats, emails, notes, reminders, and every password typed on the smartphone. You can even use it to hack your target’s camera.
All these and more data will be stored in your online account; you can access it anytime using a neatly designed control panel.
To get mSpy, follow these four simple steps:
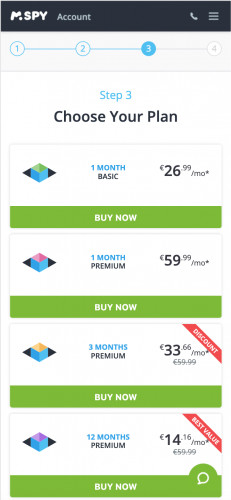
Step 1: Purchase a premium subscription on the official website
Step 2: Get detailed instructions to your email address
Step 3: Hit the download button and install the spy app on a target device
Step 4: Log in to your control panel from any device and start monitoring.
Is It Legal to Hack the iPhone Passcode?
The critical factors in determining this are a) who the device belongs to from a legal perspective, b) how old the target is, and c) how you got access to the phone.
As far as law enforcement agencies in the United States are concerned, you have every right to monitor the iPhones of your underage children to ensure they’re safe from cyberbullying or inappropriate content.
The same applies to business owners who track corporate iPhones by number. The difference is the employees must be informed about this.
When it comes to monitoring partners or other adults, it is considered an invasion of privacy and, therefore, a crime unless you’ve managed to get their written consent.
Final Say
As you can now tell, you don’t have to be a sophisticated hacker to unlock iOS devices or hack iPhone passcode. If you were worried that someone has hacked your messages, this is how they could have done it perhaps.
But still, Apple goes to great lengths to protect its customers’ confidential information, so none of the existing methods can give you a 100% success guarantee, no matter what other resources promise you.
Follow our tips, and your screen unlock success rate may skyrocket. Any questions left unanswered by this article? Let us know in the comments.
Hi I suspect my spouse is spying on my iPhone as well as in my home. It’s beyond changing passwords or updates on firmware. I am confident that this is happening because of phones heating up both in his presence and during confidential meetings. In addition my phones have consistently made beeping noises, sudden keyboard sounds, Home Screen modifications etc.
Apple support “suggests that the firmware might have been modified?” But the of course will not commit.
Two factors do not work because he is viewing texts.
The authorities are not interested.
Can you give me advice as to the type of professional to seek? A personal injury attorney, a forensic expert?
This is stalking. And has been going on for at least 4 years.
Thanks for your help.
GET A DIIFFERENT PHONE. I like my CDMA flip phone personally …